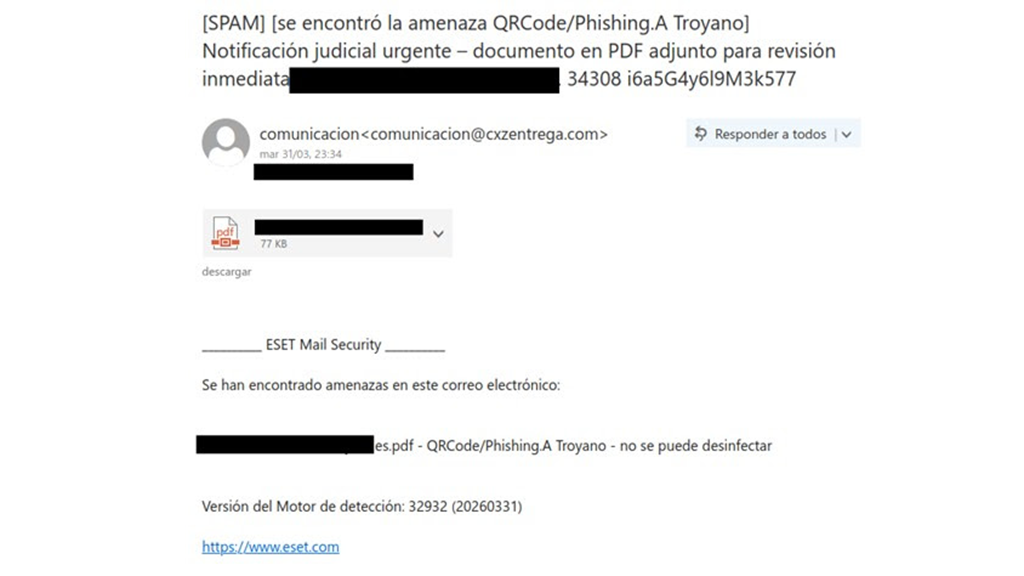
According to ESET, a new spam campaign is once again using as its subject a supposed judicial notification, though the criminals do not intend to defraud us, but to compromise the security of our system.
Recently, the company has detected in its labs a spike in activity around a particular type of emails that, posing as an official communication informing us of an urgent judicial notification, urge the email recipient to open the attached document.
What the scam involves
In the body of the message there is nothing written that would build trust in the message, so criminals rely entirely on the subject line and the content of the attached PDF to convince recipients of these emails.
In the attached PDF, you can see the supposed judicial notification referenced in the subject, with the Spanish coat of arms prominently displayed, which indicates a level of personalization of the campaign and clear targets such as Spanish citizens. It also provides both an embedded link in the button labeled “Consultar expediente” and a QR code to access the supposed summons.
A very similar campaign attributed to the Casbaneiro group (though without the QR code in the PDF) has been analyzed recently by researchers at BlueVoyant, who have studied the threat’s behavior in depth and provide technical insights about the tactics, techniques, and procedures used by the attackers.
Additionally, in our labs we have detected another campaign from the same group, but instead of using a judicial notification as the subject, it uses the sending of a résumé, including a link in the PDF to download a supposed presentation.
One notable feature of these campaigns is the efforts by cybercriminals to ensure that only targeted victims download the samples. Thus, besides using geo-fencing to ensure the malware can only be downloaded from Spain, they incorporate measures to hinder automatic analysis, such as performing a check to ensure that the one attempting to access the download is not a bot.
Once this hurdle is cleared, we are redirected to a site used to host the files that make up the first stage of the infection chain. We observe that the download has started and that the file is ready as it downloads onto the user’s system. It’s worth noting that this site is poorly designed and may raise red flags for some users, but the criminals trust that they will still obtain enough victims to make the campaign profitable.
Inside the compressed file there is only an HTA file accompanied by a folder containing a legitimate Oracle Java SE component. These kinds of files are commonly used in the early stages of the infection chain because they typically contain code that redirects to the download of the second-stage malware or the payload responsible for executing the attackers’ threat.
Inside the HTA file, there are a few lines of useful code, as almost all of the file is filler to hide a single real action, which is loading remote JavaScript from an external domain. We also find an encoded signature, which appears to be an internal identifier or marker more than functional HTML content.
The particularly relevant part of this file is the URL from which a script prepared by the criminals is loaded, a URL that is clearly visible in plain text and redirects us to the next website.
With this script the second phase of the attack is triggered, which consists of downloading and executing a VBScript file that ends up installing the Casbaneiro banking Trojan on the victim’s system, ready to collect online banking credentials when the user visits any of the sites associated with banks on the attackers’ target list.
Latin American banking trojans, and more specifically those originating from Brazil, have long been at the forefront of notable campaigns on both sides of the ocean. Over the past years we have seen how they have evolved their techniques and improved them, recently employing the ClickFix technique to mislead potential victims.