HP has published its latest Security Threat Insights Report, warning that cybercriminals are using AI to expand and accelerate their campaigns. Many prioritize cost-effectiveness and speed over technical sophistication. Although these are simple, low-resource attacks, AI-assisted campaigns are managing to bypass enterprise defenses.
The report analyzes real cyberattacks and helps organizations understand the techniques criminals use to evade detection systems and compromise device security. Based on analysis of millions of devices protected with HP Wolf Security, among the most notable campaigns identified by HP threat researchers are included:
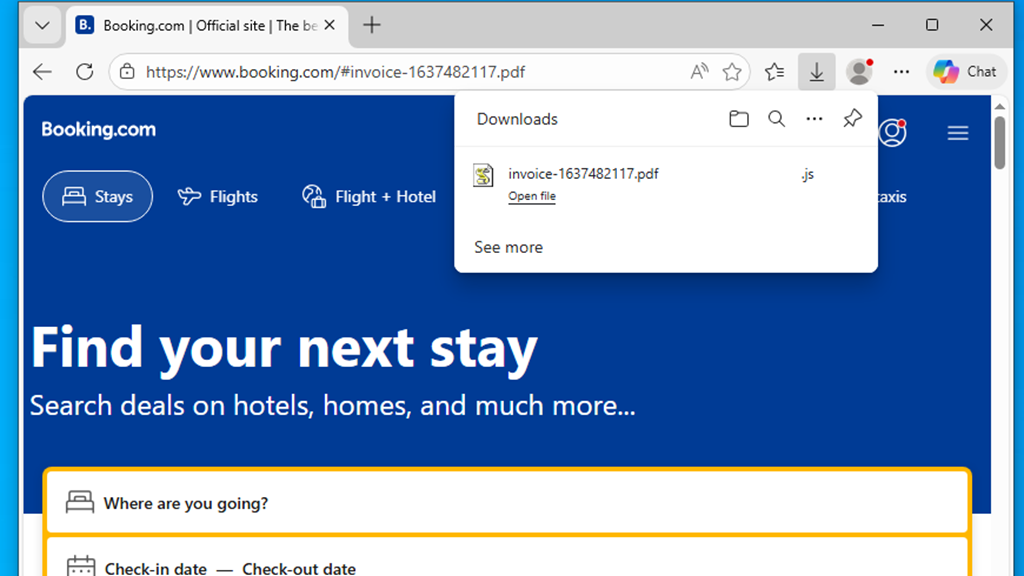
- Vibe-hacking scripts that use redirects to Booking.com: attackers are using artificial intelligence to generate ready-to-use infection scripts, known as vibe-hacking, to automate malware distribution. In one detected campaign, a link included in a fake PDF invoice triggers a silent download from a compromised website and, subsequently, redirects the victim to a trusted platform like Booking.com, with the aim of avoiding suspicion.
- Flat-pack malware accelerates campaign creation: threat actors are mounting attacks with inexpensive, ready-to-use malware components, likely purchased on hacker forums. While the lures and final payloads vary, they reuse the same scripts and intermediary installers. This allows them to create, customize, and scale campaigns with minimal effort. Researchers note that this is not a single group, but multiple actors using the same basic components.
- Malware hidden in a fake Teams installer, piggyback attack: Campaigns have also been detected that distributed malware through fraudulent search engine placement and paid malicious ads promoting fake Microsoft Teams pages. Victims download an infected installer in which Oyster Loader malware runs during the installation process. While the legitimate application installs normally, the infection goes unnoticed and grants the attacker remote access to the device.
Alex Holland, HP Security Lab’s principal threat researcher, commented: “It’s the classic project management triangle: speed, quality, and cost. Usually one of these elements is sacrificed. What we’re seeing is that many attackers prioritize speed and cost over quality. They’re not using AI to sophisticate the attacks, but to execute them faster and with less effort. The campaigns are basic, but still effective.”
More Attack Methods on the Rise
The report, which analyzes data from October through December 2025, shows how cybercriminals continue to diversify their methods to bypass traditional detection tools:
- At least 14% of email threats identified by HP Sure Click bypassed one or more gateway scanners.
- Executable files were the most popular delivery type (37%), followed by .zip files (11%) and .docx (10%).
Ian Pratt, HP’s Global Security Director for Personal Systems, noted: “AI-assisted attacks highlight the limitations of detection-based security. When attackers can generate and repackage malware in minutes, traditional defenses cannot keep pace. Rather than trying to detect every variant, organizations should reduce their exposure to risk. If they contain high-risk activities, such as opening unreliable attachments or clicking on unknown links, in isolated environments they can stop threats before they cause harm and eliminate an entire category of risk.”